Launch Your High-Paying
Cybersecurity Career
In 90 Days...
Even if you have Zero IT Experience or No Technical Degree.Master practical hacking skills & get hired.
Trusted by 10,000+ Alumni Working At:
























Request Access
Limited spots available for the upcoming cohort.
The Reality Check
Why You Are Not An Ethical Hacker Yet...
Most aspiring hackers are stuck in a cycle of passive learning and zero results. Does this sound familiar?
#1 The "Tutorial Hell" Loop
Watching hundreds of "How to Hack" videos without ever touching a real terminal. Passive consumption creates a false sense of competence.
Core concepts include confidentiality, data integrity, authentication, and non-repudiation.
The security of RSA relies on the practical difficulty of factoring the product of two large prime numbers.
The security of RSA relies on the practical difficulty of factoring the product of two large prime numbers.
The security of RSA relies on the practical difficulty of factoring the product of two large prime numbers.
#2 All Theory, No Labs
Universities teach you the history of encryption. We teach you how to fast-track breaking it. You need muscle memory, not memorization.
#3 Zero Career Guidance
Learning skills is only half the battle. Without a roadmap to navigate HR filters and technical interviews, your resume ends up in the void.
#4 Useless Paper Certs
Most "completion certificates" are ignored by recruiters. Industry demands globally recognized, proctored certifications (like CEH, OSCP), not PDF participation trophies.
#5 The "Unguided" Maze
Trying to piece together a curriculum from random blog posts is efficient at only one thing: wasting years of your life. You need a structured, battle-tested path.
The Roadmap
How You Can Finally Become An Ethical Hacker
Stop the endless loop of tutorials. Choose a structured path designed by industry experts to take you from zero to job-ready.
Tell us a little about yourself to get free guidance from our industry experts and kickstart your journey in cybersecurity — no commitment, just clarity.
CEH Masterclass | v13 AI
The Gold Standard in Hacking
Master Real-World Ethical Hacking with AI-Powered Labs
Globally Recognized, Fully Proctored Practical Certification
Become Job-Ready with AI-Enhanced Training
Official EC-Council Materials & Vouchers
Duration
4 Months
Hours
100+ Hours
Certs
3 Global Certs


Graduate Program
Comprehensive Cyber Career Foundation
Industry-Integrated AI-Powered Curriculum
Live Labs, Real Attack Simulations & Tool Mastery
Career-Launch Focus with Global Certification Pathways
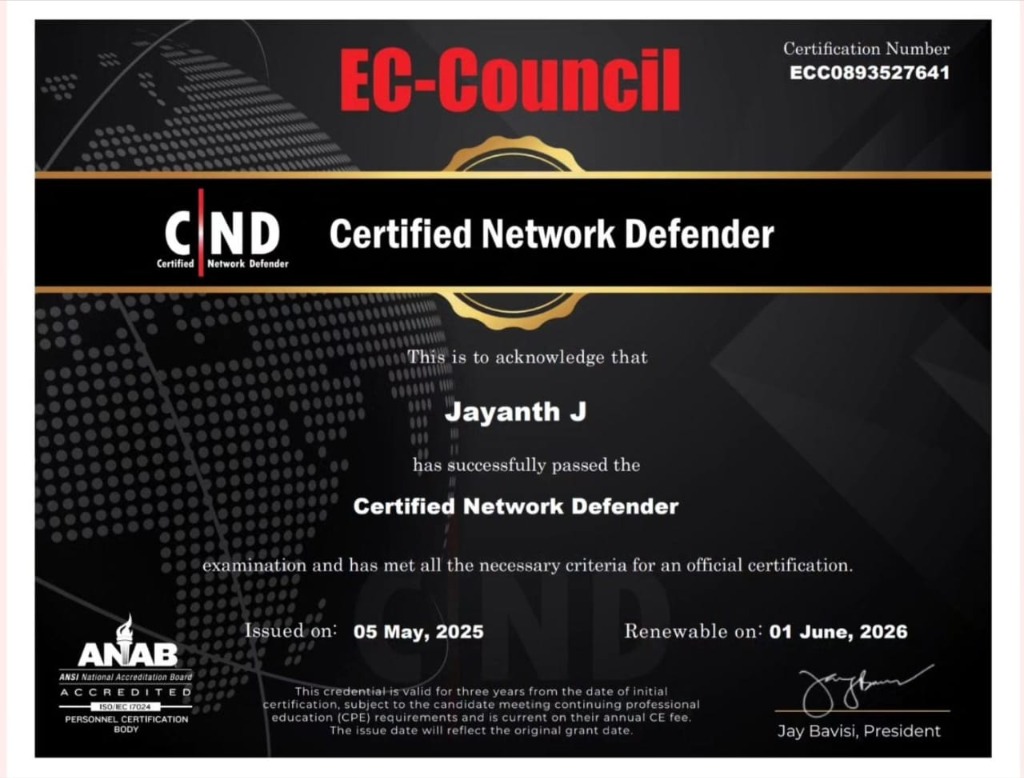
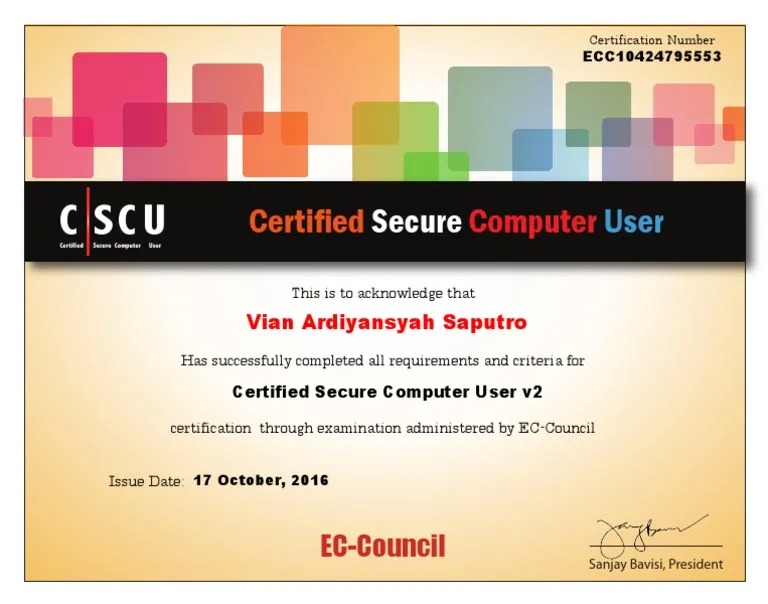
CND & CSCU Certification Modules
Duration
7-9 Months
Hours
200+ Hours
Certs
2 Global Certs
Master's Program
Advanced Cyber Leadership Training
Advanced AI-Driven Cybersecurity Mastery
Real-World Cyber Range & Enterprise Attack Simulations
Leadership Role - Focused Career Acceleration
6 Global Certifications Bundle
Duration
9-12 Months
Hours
300+ Hours
Certs
6 Global Certs


* All programs include intensive hands-on labs and placement assistance.
The Architecture of Success
Just Like How They All Did It.
Real transformations from our elite programs. From standard IT roles to high-stakes cybersecurity leadership.
"Starting as a fresher, I had no roadmap. The Masters Program gave me the hands-on skills to land a core cybersecurity role immediately. Ideally, I'd still be searching without this guidance."

Anmol Gupta
APV-DELIVERY

"Transitioning from IT management to cybersecurity felt risky, but the 200% hike proved it was the right move. The program's depth prepares you for real-world advisory roles."
Rohit Prasad
Advisor

"I was in generic tech support. This program specialized my skills. Now I'm handling technical support for a major firm with a 150% salary jump. It changed my career trajectory completely."

Snigdha S. Poonghat
Tech Support Eng.

"Software development was fine, but cybersecurity is where the future is. Validating my skills here led to a 120% hike and a core engineering role at a top firm."

Damini Ranganath
Cybersecurity Eng.

"Red teaming requires deep technical knowledge. The advanced modules here covered everything I needed to clear the SISA interview and secure a massive 300% hike."

Vaddi Paneendar
Red Teamer

"From system admin to teaching the next generation. The concepts I learned were so clear that I now mentor others. The 140% hike was just the cherry on top."

Rajiv Govind
Head Teaching Asst.
"Reaching a Director level requires more than just tools; it requires strategic understanding. This program bridged that gap for me, leading to a 160% hike."

Pranshu Tiwari
Director Security

"Managing IT is different from securing it. The transition to Associate Director at SISA was possible because of the rigorous, practical training I received here."

Abhinav Choubey
Associate Director
"Starting as a fresher, I had no roadmap. The Masters Program gave me the hands-on skills to land a core cybersecurity role immediately. Ideally, I'd still be searching without this guidance."

Anmol Gupta
APV-DELIVERY

"Transitioning from IT management to cybersecurity felt risky, but the 200% hike proved it was the right move. The program's depth prepares you for real-world advisory roles."
Rohit Prasad
Advisor

"I was in generic tech support. This program specialized my skills. Now I'm handling technical support for a major firm with a 150% salary jump. It changed my career trajectory completely."

Snigdha S. Poonghat
Tech Support Eng.

"Software development was fine, but cybersecurity is where the future is. Validating my skills here led to a 120% hike and a core engineering role at a top firm."

Damini Ranganath
Cybersecurity Eng.

"Red teaming requires deep technical knowledge. The advanced modules here covered everything I needed to clear the SISA interview and secure a massive 300% hike."

Vaddi Paneendar
Red Teamer

"From system admin to teaching the next generation. The concepts I learned were so clear that I now mentor others. The 140% hike was just the cherry on top."

Rajiv Govind
Head Teaching Asst.
"Reaching a Director level requires more than just tools; it requires strategic understanding. This program bridged that gap for me, leading to a 160% hike."

Pranshu Tiwari
Director Security

"Managing IT is different from securing it. The transition to Associate Director at SISA was possible because of the rigorous, practical training I received here."

Abhinav Choubey
Associate Director
"Starting as a fresher, I had no roadmap. The Masters Program gave me the hands-on skills to land a core cybersecurity role immediately. Ideally, I'd still be searching without this guidance."

Anmol Gupta
APV-DELIVERY

"Transitioning from IT management to cybersecurity felt risky, but the 200% hike proved it was the right move. The program's depth prepares you for real-world advisory roles."
Rohit Prasad
Advisor

"I was in generic tech support. This program specialized my skills. Now I'm handling technical support for a major firm with a 150% salary jump. It changed my career trajectory completely."

Snigdha S. Poonghat
Tech Support Eng.

"Software development was fine, but cybersecurity is where the future is. Validating my skills here led to a 120% hike and a core engineering role at a top firm."

Damini Ranganath
Cybersecurity Eng.

"Red teaming requires deep technical knowledge. The advanced modules here covered everything I needed to clear the SISA interview and secure a massive 300% hike."

Vaddi Paneendar
Red Teamer

"From system admin to teaching the next generation. The concepts I learned were so clear that I now mentor others. The 140% hike was just the cherry on top."

Rajiv Govind
Head Teaching Asst.
"Reaching a Director level requires more than just tools; it requires strategic understanding. This program bridged that gap for me, leading to a 160% hike."

Pranshu Tiwari
Director Security

"Managing IT is different from securing it. The transition to Associate Director at SISA was possible because of the rigorous, practical training I received here."

Abhinav Choubey
Associate Director




Joined 5,000+ graduates in Elite Security Roles
The Industry standard.
Zero Compromise.
Step into a high-growth secure career with the right skills, real experience, and massive market demand.
Unprecedented
Market Demand
Enter an industry with zero clutter. Cybersecurity faces a global shortage. Be the specialized talent companies hunt for.
Cybersecurity Hits
0% Unemployment
3.5 Million Unfilled
Seats Globally
Market Spike
Ethical Hackers See
150%+ Salary Surge
Master Industry-
Standard Tools
Equip yourself with the tools the pros use. Master the arsenal required to defend and attack at an elite level.

100% Stipend
Internship
Bypass the "fresher" tag by working on real-world vulnerabilities and live company projects through our guaranteed internship.
Unprecedented
Market Demand
Enter an industry with zero clutter. Cybersecurity faces a global shortage. Be the specialized talent companies hunt for.
Cybersecurity Hits
0% Unemployment
3.5 Million Unfilled
Seats Globally
Market Spike
Ethical Hackers See
150%+ Salary Surge
Master Industry-
Standard Tools
Equip yourself with the tools the pros use. Master the arsenal required to defend and attack at an elite level.

Choose Your Path
Detailed breakdown of our elite cybersecurity programs to help you decide.
Masterclass
Graduate
Masters
Schedule Options
Weekday (Tue-Fri): 2 hrs/dayWeekend (Sat-Sun): 4 hrs/day
| Features | Masterclass | Graduate | Masters |
|---|---|---|---|
| Start Date | 5th of Every Month | 5th of Every Month | 5th of Every Month |
| Duration | 4 Months | 7-9 Months | 9-12 Months |
| Mode | Classroom + Live Online | Classroom + Live Online | Classroom + Live Online |
| Total Hours | 100+ Hours | 200+ Hours | 300+ Hours |
| Membership | 6 Months Membership | 2 Years | 2 Years Support |
| Global Certification | 3 Global Certifications | 2 Global Certifications | 6 Global Certifications |
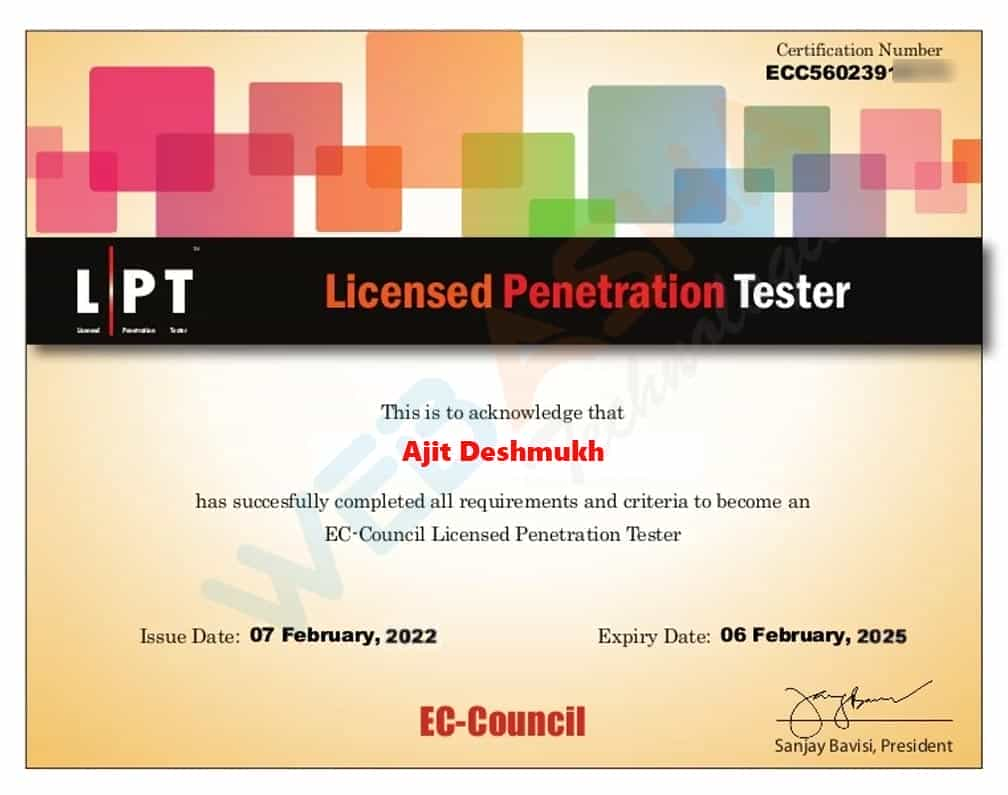
| EC Council Certifications | CEH v13, CEH Practicals, CEH Masters | CSCU, CND v3 | CSCU, CND v3, CEH v13, Cpent v2+LPT, CHFI v11 |
| Ehack Academy Certifications | Nil | Cyber Security Fundamentals, Ethical Hacking, Penetration Testing / Digital Forensics, OWASP 10 | Cyber Security Fundamentals, OWASP 10 |
| Career Development Training | Nil | Personality Development & Soft Skills | Personality Development & Soft Skills |
| EMI Options | Starting at ₹28,750 | Starting at ₹29,750 | Starting at ₹50,000 |
| Placement Support | Included | Included | Included |
| Internship | Included | Included | Included |
| 24/7 Labs | Included | Included | Included |
Schedule Options
Weekday (Tue-Fri): 2 hrs/day|Weekend (Sat-Sun): 4 hrs/day
Speak to our career counselors starting at ₹0
Looking for a Specific Certification?
Beyond our flagship programs, we offer dedicated training for the industry's most sought-after global credentials.
Frequently Asked Questions
Everything you need to know about starting your high-paying career in cybersecurity.
Still have a specific query? We're here to help.
The Blueprint is Ready.
Now, It's Your Turn to Build.
You’ve seen how others engineered their success. We have the architecture, the labs, and the placement engine ready for you.
Work on Live Projects
Gain hands-on experience with real-world scenarios and labs.
Get Hired Faster
Our placement team works with you until you land your first job.
Request Your Blueprint
Fill in your details and our career architects will reach out within 24 hours.